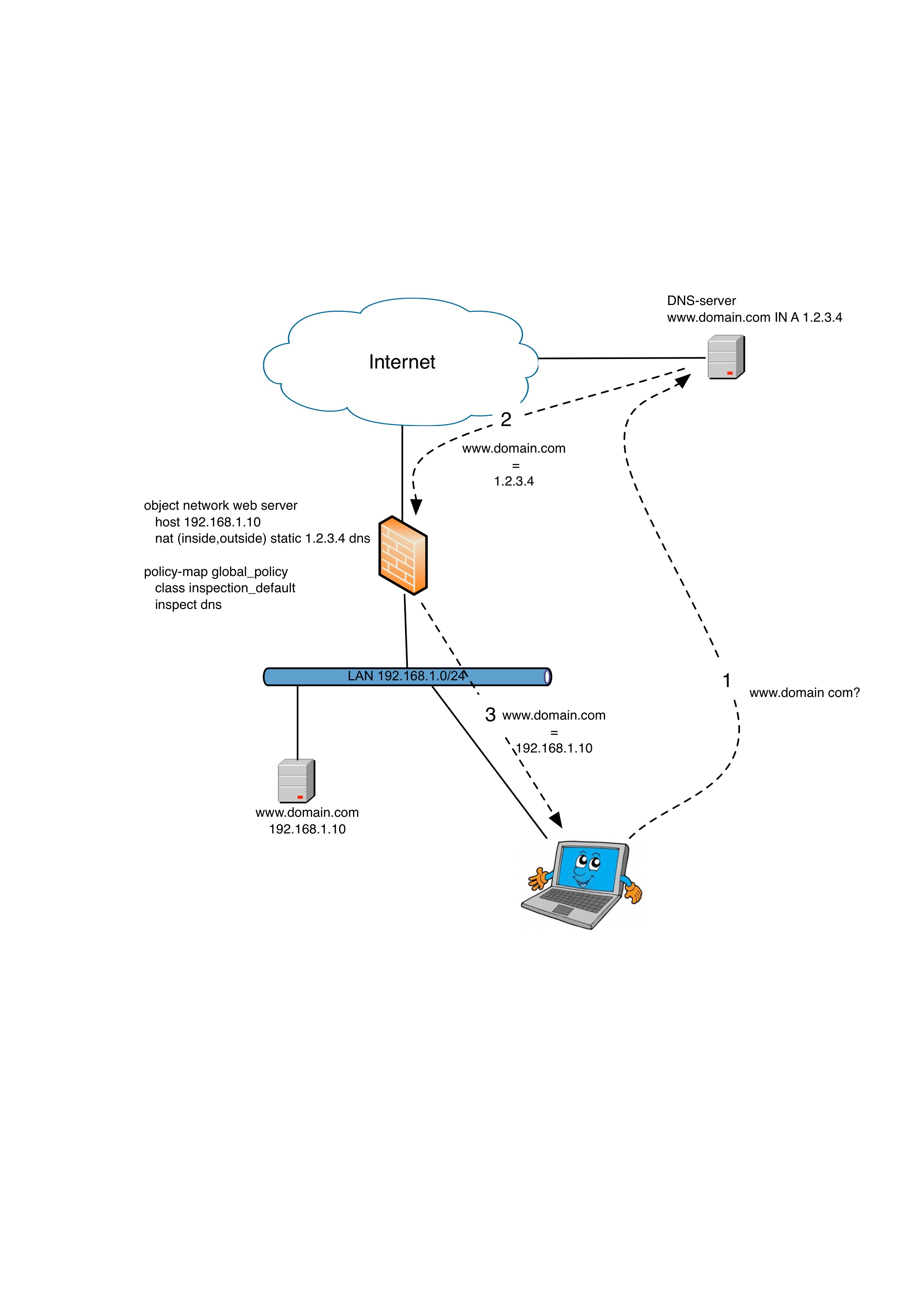
Issue: Your internal clients tries to reach an internal server but since they resolves the address of the server from an external DNS-server they will get a public IP.
Solution: DNS Doctoring.
In the example below your client is on the internal 192.168.1.0/24-network. When looking up the hostname for the webserver www.domain.com it resolves to the public ip of 1.2.3.4. When the client on the inside tries to reach the NAT:ed IP 1.2.3.4 the ASA will get confused and there will be no response.
There is a NAT already configured mapping the public ip 1.2.3.4 to the internal IP 192.168.1.10. The trick here is to add the keyword “dns” to the end of the static NAT-statement. This will inspect all DNS-traffic goingthru the ASA and when it seed a DNS-response of 1.2.3.4 sent to an internal host it will modify the packet so that the response will be 192.168.1.10 from the clients point of view.
The only thing to remember here is that you need to do DNS inspection in the firewall for this to work. Or else it will not. 🙂
So the configuration will be:
object network web server
host 192.168.1.10
nat (inside,outside) static 1.2.3.4 dns
!
policy-map global_policy
class inspection_default
inspect dns
If you are a GUI-type of human you set the DNS-setting by finding your specific NAT-statement (for the public webserver) under Configuration -> Firewall -> NAT-rules and in the window for your NAT hit the “Advance”-button. There you find the “Translate DNS replies for rule”.
The inspection is found under Configuration -> Service Policy rules -> Global Policy -> inspection_default (double click it) -> Rule Actions -> Protocol Inspection and make sure that the DNS checkbox is set.
And don´t you forget to write mem! 😉



Whats up! I simply want to give a huge thumbs up for the great information you could have here on this post. I might be coming back to your blog for more soon.