I often get into discussions with customers about the active/active feature of Cisco firewalls (ASA/FWSM). There seems to be a lot of confusions regarding the possible redundancy scenarios.
The short story first: The only scenario when active/active can be done is when you have 2 physical units and at least 2 virtual firewalls (contexts) configured.
But we start from the beginning…
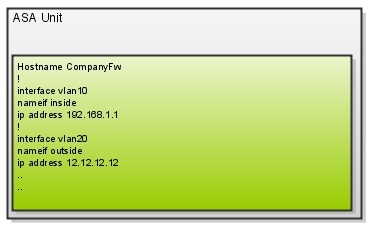
Single Box – Single Context
The most common solution for small companies is having one single firewall without any redundancy. There is not much to say about it…
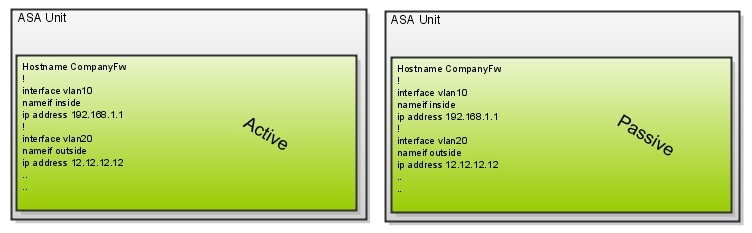
Dual boxes – Single Contexts
By adding another box you get a active/passive-failover, also known as hot standby. The primary box is doing all the work and the secondary just waits to stand in in case of a failure of the primary. There is no load-sharing.
The usage for this is an organisation that has no need for multiple contexts but wants their firewall to be redundant.
Single Box – Multiple Contexts
If there is need for multiple context, the firewall can be configured so. Two (or more) different configurations can share the same physical hardware. They can also share interfaces with some exemptions. Each context can have different administrative profiles configured so that a specific person can configure only one context.
Example: Company A and Company B shares a common firewall. Each company has their specific security policies and are each administered separately.
Dual boxes – Multiple Contexts
By extending the previos scenario with duplicated hardware one can get a redundant solution. With both contexts active on the left hardware this unit will handle all traffic for both of them. In case of a hardware-failure both contexts will become active on the other unit.
Example: The need for high-available firewall-functionality made the company AB to invest in redundant firewalls. They need to have multiple security policies administered by each companys respective IT-department. It all runs in Unit 1, while Unit 2 is configured as a hot-spare.
Dual boxes – Multiple Contexts balanced
If one context is active in one hardware and another context in the other one you will get a load-balanced-ish solution. Normal case is that the left unit handles Department A context and the right unit takes care of all traffic for Department B. In case of a hardware failure on either unit, the context(s) that were active in the failed unit “moves” to the other hardware.
Scenario: To gain performance company AB have distributed the placement of each contexts active unit. The left unit takes care of Department A:s context and the left one handles the context of Department B. Each unit is hot-spare for respective context.
Important notes:
- The only case when “active/active” can be built is when you have multiple contexts.
- There is no load-sharing done “within” a context. That means that if traffic going thru the green context it will suck all resources out of the left unit without any “help” from the right unit.
- These multiple-contexts-scenarios also applies to when having more than two contexts. For example, if there are 5 contexts, 0, 1, 2, 3, 4 or five of them can be active in each unit. It´s all configurable. This configuration is done by putting contexts in failover-groups and this config is the only difference between the two last scenarios above.
Final words:
A Cisco ASA-solution without multiple contexts can never be active/active.